

What is Phishing?
Phishing is a fraudulent act performed by a threat actor attempting to gain information from the recipient in an email or communication channel. Some common examples include users clicking on a link, opening a malicious attachment, or redirecting to a website designed to capture credentials.
As technology progresses into the future and interconnectivity becomes more viable, cybersecurity risks increase. In the 2019 Data Breaches Statistics Report, the Office of the Australian Information Commissioner (OAIC) identified that 62% of all data breaches are malicious or criminal attacks. This mostly affects the health, finance, legal/accounting, education and retail sectors with the impact extending from the business to its vendors and clients. In 2019, phishing alone has accounted for 90% of data breaches.
According to Ponemon Institute’s ‘Cost of a Data Breach Report’, “the cost for a company that suffers a data breach is $3.92million.” More alarmingly, “36% of the cost of a data breach comes from the loss of business stemming from loss of customer trust after a cyber incident.”
A Feat for Small Businesses
Many small businesses put cybersecurity on a back burner due to its perceived costs. However, the costs of losing data and consumer trust are much higher than spending on a proactive cybersecurity strategy for the business.
Sometimes it only takes a few sit-down sessions to perform risk assessments on the many ways hackers or cybercriminals can penetrate the system. After which, a company can create an informed security strategy that suits them best.
The Evolution of Phishing Attacks
The first-ever phishing attack transpired in 1994 when a hacker targeted AOL’s direct messaging system. They were able to obtain personal credentials by sending a direct message to trusting users, catching them off-guard (as the term phishing was not even a common term then).
From then on, phishing has taken on many forms. With success reliant on human error and vulnerability, hackers have always sought ways to make their way through sensitive data. So even with the existence of email spoofing software, proxy servers, and anti-phishing software, no company is 100% safe from a cyberthreat.
Threat actors are continually adjusting their tactics to make their way past a robust Secure Email Gateway (SEG) by familiarising themselves with the file types that get blocked. Cofense™, a global leader in intelligent phishing defence solutions, has observed 90% of user-reported emails these days are in environments using secure email gateways!
The Types of Phishing
-
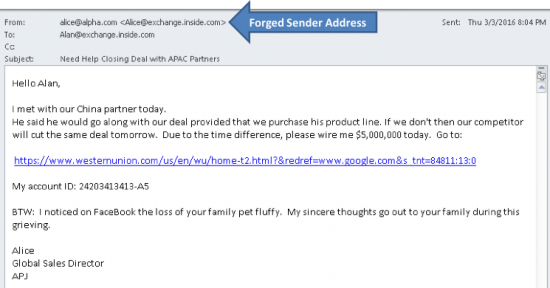
Email Spoofing
This refers to the forgery of an email address which leads the recipient to think it was sent from a legitimate source. These forgeries are easier to identify when using an email client, however, mobile devices don’t always display the full email, showing only the name of the sender.
SOURCE: Cisco
-
Spear Phishing
The most common type of email spoofing is spear phishing. Leveraging on familiarity, this type of spoofing misleads the recipient into thinking that the email was sent by a person of authority in their organisation. Spear phishing often isn’t a random attack, but a purposeful one — done with the aim of financial gain, trade secrets or military information.
A whaling attack is a specific type of spear phishing that attacks high-level employees or senior executives within an organisation. If executed, whaling makes sense as It becomes easier to reach the goal of stealing a large amount of money straight from the people who have the access and power to authorise payments.
A Business Email Compromise (BEC) is an example of an online scam that makes use of spear phishing. In this scenario, a threat actor pretends to be an employee to deceive a colleague, customer, or vendor into giving confidential information or money. These email messages can easily bypass the SEG since this tactic doesn’t include links or attachments. According to Cofense, who provides deep research and understanding of the phishing threat landscape to help companies uncover and respond to phishing attacks fast, there has been a recent shift towards payroll diversion – sending a HR person instructions to change the direct deposit as if the request was from a real employee.
-
Domain Spoofing & Cloned Phishing (Pharming)
Pharming, a type of phishing also known as domain spoofing or cloned phishing, is where a hacker redirects users from a legitimate site to fraudulent one and tricks them into using their credentials to attempt to log-in. They often use previously-sent emails — only changing one or two of the embedded links into a malicious one.
-
Search Engine Phishing
A newly-evolved type of phishing, search engine phishing is a type of cyberattack where fraudsters create fake sites offering cheap products or bargains and get it indexed by search engines. Appearing on the search engine page just like any other result, these websites will only lure visitors into buying fake products — effectively taking their personal information and money. Some examples of search engine phishing are discount and job offers.
-
Credential Phishing
This is a form of cyberattack which entails gaining access to legitimate login credentials to enter cloud-hosted apps such as Office365, OneDrive, LinkedIn, and DocuScan.
6 Ways to Protect Your Business from Email Phishing
Being familiar with the most common types of phishing is a step in the right direction towards protecting a business. The next step is to cascade this information down to other members of the organisation to create a strategic and collective solution to combat and prevent phishing attacks from taking place.
-
Train employees to identify the red flags early on.
While there are some obvious ways to detect a fraudulent email, others require more attention and scepticism. As such, it’s best practice to educate and train employees to watch out for the following tactics and report anything suspicious to their security team:
- Grammatical errors: As phishing tactics have evolved through the years, experts have learned that people in authority are more likely to commit spelling errors or typos, but not so many grammatical errors. Hackers would also only perform spell-checks, often overlooking the unnatural-sounding language used in emails. However, the scepticism shouldn’t end here; the cyberattack space is beginning to see less of this as hackers are getting more creative and better at crafting emails.
- Scare tactics: these types of emails trick the recipient into thinking that their computer has been infected or an account has been compromised. It has been effective thus far as it creates an unwarranted sense of urgency for the recipient.
- Dangerous and sketchy attachments: Threat actors attach malicious files into emails to get the code into the recipient’s system. The most dangerous file extensions include .exe, .jar, .bat, .cmd, and .vbs. They continue to evolve their tactics to include links within a PDF document that can easily bypass the SEG.
Besides watching out for these, checking for website security should be part and parcel of every employee’s cybersecurity training.
Keep an eye out for HTTPS and look for the SSL certificate. An HTTPS is a secure version of HTTP (hypertext transfer protocol) which prevents communication from being accessed by anyone but you and the website you are accessing. On the other hand, an SSL certificate is an additional layer to ensure security (apart from the HTTPS). This will allow you to double-check the website’s certificate credentials. Most browsers will give you access to this information by clicking a corresponding ‘View Certificate’ button.
-
Deploy anti-virus solutions and spam filters.
With cybersecurity threats ever-changing, hackers always go after the vulnerable sides of businesses whenever they can. Deploying an anti-virus solution adds in a layer of protection on top of a foolproof employee cybersecurity training.
For extra security, a spam or email filter solution will act as an anti-virus system within the mail inbox. As such, it is in charge of detecting emails with malicious links, attachments or spam in general.
Similarly, looking for trust badges or seals from well-known cybersecurity and/or anti-virus companies should be part of employee training. It’s a good indication that websites have taken the extra mile in securing their sites.
-
Always update company passwords.
Companies should also proactively enforce policies for a regular password change. In the United States, most companies have a policy that requires a password change every 90 days. However, the National Institute of Standards and Technology’s (NIST) password guidelines don’t require users to change passwords after a certain period anymore. Instead, new passwords should only be changed following a data breach or an equivalent compromise thereof.
As an alternative solution, make sure passwords are strong, long and use two-step or multi-factor verification. According to LastPass, after setting a strong complex password, these are the other times it should be changed:
- Following a security incident or notification of a third-party data breach
- When credentials are entered into a malicious website
- When there is a malware in devices and/or software
- When there is shared access to an account with a person who no longer uses the login (e.g., an employee leaving the company)
- When the password hasn’t been changed for over a year (especially if multi-factor authentication isn’t present)
-
Encrypt all sensitive company information and files.
Encryption is a digital form of cryptography that scrambles messages via mathematical algorithms. The only parties who possess the sender’s cipher/key will be able to decode the message.
Depending on what the business needs, encryption can be done on a file/folder level, in large volumes, or full-disk (all files, sensitive or not, will be encrypted). Some modern operating systems (OS) will have built-in encryption programs (such as OS X, Windows, Linux). For bigger organisations, investing in third-party encryption programs might prove to be a more viable option.
-
Use secure browsers.
Think of the browser as the keeper of all information whenever a person visits the world wide web. It stores large amounts of information that can be exploited when not managed properly. A person’s cookies, credentials, browsing history, and other related information are at stake. Regardless of which browser you choose, never save your username and password in the browser when prompted.
Some popular browsers have modes in which they can provide better security. The new Firefox browser, for instance, offers modifications to tighten protection against hacks and malware.
-
Identify the anti-phishing solution that’s right for you.
Ideally, an anti-phishing solution should be able to train and condition employees to recognise phishing attacks. It relies on changing human behaviour to take a proactive approach towards preventing and combating phishing.
Besides installing powerful anti-virus software, having an anti-phishing solution creates the last line of defence against hackers and malware. Both Cofense PhishMe™ and Cofense Reporter™ solutions empower employees to be resilient against phishing by training them to identify attacks and then report it. This allows them to communicate threats to the organisation for further investigation. Cofense also provides solutions for an organisation’s Incident Response teams to quickly defend against a phishing incident with Cofense Triage™ and Cofense Vision™.
Phishing Attacks Only Become Successful Because of Human Error
In the past year, more than 99% of data breach attacks relied on human error to penetrate systems. This is a call to strengthen human training to fight these attempts by equipping them with the right knowledge and tools.
Increasing awareness amongst employees empowers them to take responsibility. In doing so, they play a role in the protection of important company data — effectively becoming keepers of productivity flow in the business.
Author
Marcus Bartram, Partner at Telstra Ventures

Marcus is a founder and General Partner of Telstra Ventures. Prior to this he held various executive and senior roles in Telstra, Citigroup, nscglobal and Honeywell in Australia and the UK.
Marcus invests in disruptive enterprise software, telecoms and cyber-security entrepreneurs that are starting to scale their companies. Investments made to date include Anomali, AttackIQ, Auth0, Cohere Technologies, Cofense, Crowdstrike, Elastica (ACQ:BlueCoat), Headspin, ipSCAPE, Matrixx Software, Dimmi (ACQ:TripAdvisor), vArmour and Zimperium.
Marcus received an MBA from the University of Oxford, UK and a Bachelor or Engineering (Electrical and Electronic, hons) from the University of Adelaide, Australia.